by Travis Goodspeed <travis at radiantmachines.com>
concerning research performed in collaboration with
Sergey Bratus, Ricky Melgares, Rebecca Shapiro, and Ryan Speers.
The following technique is a trick that some very good neighbors and I present in Packets in Packets: Orson Welles' In-Band Signaling Attacks for Modern Radios (pdf) at Usenix WOOT 2011. As the title suggests, Orson Welles authored and implemented the attack in 1938 as a form of social engineering, but our version acts to remotely inject raw frames into wireless networks by abuse of the PHY layer. As that paper is limited to a formal, academic style, I'd like to take the opportunity to describe the technique here in my people's native language, which has none of that formal mumbo-jumbo and high-faluttin' wordsmithin'. This being just a teaser, please read the paper for full technical details.
The idea is this: Layer 1 radio protocols are vulnerable injections similar to those that plague naively implemented SQL websites. You can place one packet inside of another packet and have the inner packet drop out to become a frame of its own. We call the technique Packet-in-Packet, or PIP for short.
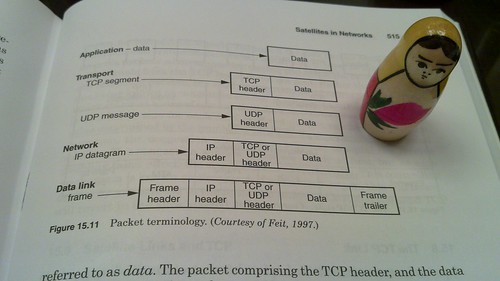
As I've mentioned in my article on promiscuously sniffing nRF24L01+ traffic, every modern digital radio has a Layer 1 form that consists of a Preamble, followed by a Sync, followed by a Body. The Body here is Layer 2, and that is the lowest that a normal packet sniffer will give you. (Keykeriki, Ubertooth, and GoodFET/NRF give a bit more.)
In the specific case of IEEE 802.15.4, which underlies ZigBee, the Preamble consists of the 0 symbol repeated eight times, or 00000000. The Sync is A7. After that comes the Body, which begins with a byte for the length, a few bytes for flags, the addresses, and some sort of data. Suppose that an attacker, Mallory, controls some of that data, in the same way that she might control an HTTP GET parameter. To cause a PIP injection of a Layer 2 packet, she need only prepend that packet with 00000000A7 then retransmit a large--but not unmanageably large--number of times. I'm not joking, and I'm not exaggerating. It actually works like that.
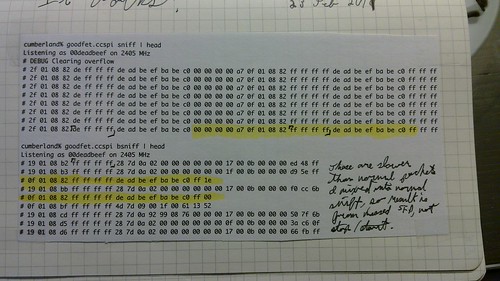
Below is a photograph of the first packet capture in which we had this technique working. The upper packet capture shows those packets addressed to any address, while the lower capture only sniffs broadcast (0xFFFF) messages. The highlighted region is a PIP injection, a broadcast packet that the transmitter intended to only be data within the payload of an outer packet.
How it works.
When Alice transmits a packet containing Mallory's PIP to Bob, Bob's interpretation can go one of three ways, two of which are depicted in the diagram below. In the first case, as shown in the left column, Bob receives every symbol correctly and interprets the packet as Alice would like him to, with Mallory's payload sitting harmlessly in the Body. In the second case, which is not depicted, a symbol error within the Body causes the packet's checksum to fail, and Mallory's packet is dropped along with the rest of Alice's.
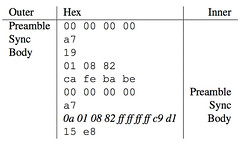
The third interpretation, shown above in the right column, is the interesting one. If a symbol error occurs before the Body, within the Preamble or the Sync, then there's no checksum to cause the packet to be dropped. Instead, the receiver does not know that it is within a packet, and Mallory's PIP is mistaken as a frame of its own. Mallory's Preamble and Sync will mark the start of the frame, and Mallory's Body will be returned to the receiver.
In this way, Mallory can remotely inject radio frames from anywhere on the network to which she can send her payload. That is, this is a PHY-Layer radio vulnerability that requires no physical access to the radio environment. Read the WOOT paper for complications that arise when applying this to IEEE 802.11, as well as the conditions under which a PIP injection can succeed on every attempt.
War of the Worlds
In 1938, Orson Welles implemented a similar exploit as a form of social engineering in order to cause panic with his War of the Worlds (mp3, transcript) performance.
Recall that PIP injection works by having the victim miss the real start of frame marker, then fraudulently including another start of frame marker inside of the broadcast. As per the FCC requirements of his time, Orson begins with a real start of broadcast marker:
ANNOUNCER: The Columbia Broadcasting System and its affiliated stations present Orson Welles and the Mercury Theatre on the Air in The War of the Worlds by H. G. Wells.
(MUSIC: MERCURY THEATRE MUSICAL THEME)
ANNOUNCER: Ladies and gentlemen: the director of the Mercury Theatre and star of these broadcasts, Orson Welles . . .
ORSON WELLES: We know now that in the early years of the twentieth century this world was being watched closely by intelligences greater than man's and yet as mortal as his own. We know now that as human beings busied themselves about their various concerns they were scrutinized and studied, perhaps almost as narrowly as a man with a microscope might scrutinize the transient creatures that swarm and multiply in a drop of water. With infinite complacence people went to and fro over the earth about their little affairs, serene in the assurance of their dominion over this small spinning fragment of solar driftwood which by chance or design man has inherited out of the dark mystery of Time and Space. Yet across an immense ethereal gulf, minds that to our minds as ours are to the beasts in the jungle, intellects vast, cool and unsympathetic, regarded this earth with envious eyes and slowly and surely drew their plans against us. In the thirty-ninth year of the twentieth century came the great disillusionment.
It was near the end of October. Business was better. The war scare was over. More men were back at work. Sales were picking up. On this particular evening, October 30, the Crosley service estimated that thirty-two million people were listening in on radios.
That introduction is two minutes and twenty seconds long, and it was scheduled to begin while a popular show on another station was still in progress. Many of the listeners tuned in late, causing them to miss the Sync and not know which show they were listening to, just as in a PIP injection! What follows is thirty-eight minutes of a first act, without a single word out of character or a single commercial message from a sponsor. The play begins in the middle of a weather report, followed by repeated false station and show announcements, a few of which follow.
We now take you to the Meridian Room in the Hotel Park Plaza in downtown New York, where you will be entertained by the music of Ramón Raquello and his orchestra.
From the Meridian Room in the Park Plaza in New York City, we bring you the music of Ramón Raquello and his orchestra.
Ladies and gentlemen, we interrupt our program of dance music to bring you a special bulletin from the Intercontinental Radio News.
We are now ready to take you to the Princeton Observatory at Princeton where Carl Phillips, or commentator, will interview Professor Richard Pierson, famous astronomer.
Good evening, ladies and gentlemen. This is Carl Phillips, speaking to you from the observatory at Princeton.
Just a moment, ladies and gentlemen, someone has just handed Professor Pierson a message. While he reads it, let me remind you that we are speaking to you from the observatory in Princeton, New Jersey, where we are interviewing the world- famous astronomer, Professor Pierson.
By repeatedly lying to the listeners about the station and the program, Welles was able to convince them that they were listening to legitimate news broadcasts of an alien invasion. Ensuring that the listener missed the starting broadcast announcement breaks the encapsulation that was intended to prevent such confusion, just as a PIP injection relies upon the start of frame to be missed in order to break OSI model encapsulation.
How the hell did this happen?
This class of vulnerability is a really, really big deal. An attacker can use it to inject raw frames into any wireless network that lacks cryptography, such as a satellite link or an open wifi hotspot. Not only that, but because the injection is remote, the attacker needs no radio to perform the injection! Not only that, but this vulnerability has sat unexploited in nearly every unencrypted digital radio protocol that allows for variable frame length since digital radio began! So why did no one notice before 2011?
Packet in Packet injection works because when Bob forwards a wrapped string to Alice over the air, he is trusting Mallory to control the radio symbols that are broadcast for that amount of time. The potential for abusing that trust wasn't considered, despite communications experts knowing full well that sometimes a false Sync was detected or a true Sync missed. This is because a symbol error in the Sync field causes the packet to be implicitly dropped, with the same behavioral effect that would be had if the error were later in the packet and it were explicitly dropped. Except when faced with a weaponized PIP injection, nothing seems strange or amiss. Sync errors were just a nuisance to communications engineers, as we security guys were staying a few layers higher, allowing those layers of abstraction to become boundaries of competence.
That same trust is given in wired networks and busses, with the lesser probability of missing a Sync being the only defense against PIP injection. Just as PIP has shown that unencrypted wireless networks are vulnerable even when the attacker is not physically present, I expect wired networks to be found vulnerable as soon as an appropriate source of packet errors is identified. Packet collisions provide this in unswitched Ethernet networks, and noisy or especially long links might provide it for more modern wired networks.
If I've not yet convinced you that this attack is worth studying, I probably won't be able to. For the rest of you, please print and read the paper and extend this research yourself. There's a hell of a lot left to be done at the PHY layer, and it might as well be you who does it.
Thank you kindly,
--Travis Goodspeed

232 comments:
1 – 200 of 232 Newer› Newest»Very nice work! This illuminates the path to a lot of interesting possibilities
Excellent work and as always a great presentation, you really do amazing HW things. One small, small nitpick; In the third para it reads "The idea is this: Layer 1 radio protocols are vulnerable injections". I guess the word "to" is missing.
Aloha!
One thing the paper does not address/suggest is how to solve the situation.
How should we add injection filtering, authentication and integrity protection on L1? Esp without seriously complicating the protocols and open up for other attacks.
Upper level layers somehow assumes that they can trust the lower levels and security mechanisms are placed at the higher levels (IPsec, WPA, HTTPS or even 802.15.4 CCM* on L2)
Fascinating. Would data-whitening affect this attack?
Interesting post, and a really clever name for it! ZigBee is clearly vulnerable to this attack, but I'd be shocked if the problem is widespread--I worked on this sort of system many years ago, and it was common practice to include a "scrambler" in the design--the final step before handing the bit stream off to the transmitter was to "scramble" it by looking at the bit stream and adjusting it, both so it had enough 0-1 and 1-0 transitions to insure timing recovery on the far end... and to make sure you never transmitted anything that looked like a framing signal. The scrambler wasn't cryptographic--it was simple, deterministic, and easily reversible. Using your SQL injection analogy, it was the equivalent of "escaping" troublesome sequences in the bit stream.
ZigBee clearly doesn't incorporate a scrambler in it's design, but I'd hope that this common design practice of 20-30 years ago wasn't completely forgotten...
Howdy Forrest,
You are right that scramblers can be troublesome, but at least in 802.11B, they weren't too much trouble.
When injecting at the same data rate, the scrambler is self-synchronizing and self-correcting. 802.11B specifies a preamble and Sync in the pre-scrambled state, and *any* scrambled version of them is acceptable, so the attacker doesn't need to know the scrambler state and no scrambler state will hurt the odds of injection.
When injecting a 1Mbps packet from within the body of a 2Mbps packet, which is more common, the scrambler does become a pain in the neck. Luckily, its state is only 7 bits, so at worst it only reduces the odds of injection 128 times. I've posted scrambler source code at https://github.com/travisgoodspeed/80211scrambler for Verilog.
Cheers,
--Travis
An attacker can use it to inject raw frames into any wireless network that lacks ... digitalframewifi.blogspot.com
It seems to be obvious the possibilities that the PiP attack creates, but I'm struggling to come up with any truly threatening or useful scenarios. Specifically in 802.3 (Ethernet) which was suggested for future work in the paper because of the "staggering implications." Would anyone be so kind as to elucidate the possibilities for me?
I have honestly never read such overwhelmingly good content like this. I agree with your points and your ideas. This info is really great. Thanks.
Point Cloud to BIM conversion
Point Cloud to BIM conversion in USA
This is Very very nice article. Everyone should read. Thanks for sharing. If any business is looking for web design or website design and web development services in Singapore. Here, you will find best web design packages.
Looking for some phone tracking application? Recommend to try out this app to track phone without them knowing. It's good.
Wow. This is an interesting blog to read. It actually familiarised me with various qualities that a true and genuine assignment provider must have. Now, I understood that the work of an assignment expert is not just to provide assistance with the assignment, but also to clarify the topics and concepts related to the assignment that can become hindrance for students when they do their assignments.
This is the reason I have always chosen My Assignment Services as my assignment writer. They have not only helped me with my assignments but also provided me free samples and reference solutions that helped me a lot while doing my assignments myself. Moreover, the free copy of the Turnitin report that they always provide me with the work is what validates their authentic work. In addition to this, I have often made use of their live one-on-one session to get in touch with their experts even after they submitted the whole work. This helped me a lot to clarify the concepts even better.
So, whenever you search for the most reliable assignment provider, My Assignment Services is surely one of the best options to choose from
Thanks for sharing such a nice Blog.I like it.
norton com/setup
norton.com setup product key
renew norton
enter norton product key code to activate
norton installation with product key
enter norton product key code to activate
Thanks for the share! Good luck.
Buy now office stationery online at low prices only in officeshoppie.com. OfficeShoppie is the best Office stationery supplies in Bangalore, Office stationery supplier in Bangalore, Office stationery online at low prices, Notepads | Dairies | Planners, Office cleaning products supplier in Bangalore, Housekeeping products supplier in Bangalore, online Tissues supplier in Bangalore, Hygienic Tissues for office, Office cleaning agents supplies in Bangalore, Cleaning agents supplier in Bangalore, Office snacks supplier in Bangalore, Office snacks supplies in Bangalore, Snacks for office,Office snacks delivers in Bangalore, Office pantry supplier in Bangalore
Office pantry supplies in Bangalore, Office pantry items supplies in Bangalore, Office Pantry items supplier in Bangalore, Corporate gifting supplier in Bangalore, Corporate gifts supplies in Bangalore, Office gifts supplier in Bangalore, Office gifts supplies in Bangalore, gifts and awards supplier in Bangalore, Gifts and awards supplies in Bangalore, Wood trophy's supplier in Bangalore, Wooden trophy's supplies in Bangalore. Office celebrations items supplier in Bangalore, Office celebration items supplies in Bangalore. Office Crockeries supplier in Bangalore, Office Crockeries supplies in Bangalore.
Get Top 5 Website Designing Company in Delhi for Dynamic Website Designing and also get SEO Services at Ogen Infosystem.
Top 5 Website Designing Company in Delhi
Nice post. Kindly keep updating us.
web development company Singapore
Mobile Application Development Singapore
Freelance Web Development Singapore
Thanks for sharing such a nice Blog.I like it.
diggerslist
trover
eset
ignitiondeck
misterpoll
wonderhowto
I adore looking at and I conceive this website got some truly utilitarian stuff on it!
www.freesitemaker.net
That is why I prefer to use websites that are created by corporations that are reliable. Check a review of Gator web builder, for example.
Group buy seo tools india
Best seo group buy tools
Group seo tools buy
Group seo tools
Seo group buy
Group buy seo tools
Group buy seo tools india
Your post is not easy, but very interesting!
Please check out my article about one the most modern spying apps - Highster mobile.
Nice Information. Thanks for sharing this Post. Are you looking for web design and mobile app development for your company or business please contact Calvin Seng your freelance website designer and mobile app developer in Singapore. Structure your business website and get web hosting FREE.
Click the below links know more the offers:
App Development
Online Marketing SEO Singapore
Branding Design Singapore
Web Designer Singapore
Digital Marketing Agency in Singapore
Web Developer Singapore
BaZi Branding Singapore
新加坡专业网站建设公司
新加坡网页设计
Thank you for the details and if you are interested in knowing
Jonathan Chee Sze Chiang
Jonathan Chee Sze Chiang Trademark
jonathan chee sze chiang
feng shui class
office feng shui
home feng shui
feng shui service
feng shui master
Aegean Cruises is an officially licensed, government regulated and established Yacht Charter and Tourism company based in Alimos Marina, Athens.Its sound really good. I am very time read your blog.Thanks for the sharing this blog with us.Keep it up.
Rent a yacht in Greece
Yacht charter Greece
Yacht hire Greece
yachting in Greece
Before reading your post, I was stuck with the bug exploit. Encoders encoded the buffer successfully and exploit was completed but no session was created. But now I'm happy because everything gone right. Assignment writing services
Thank you so much for this excellent Post and all the best for your future. I hope you and we will be sharing more thoughts and keep writing more like this one.
office.com/setup
mcafee.com/activate
thanks for sharing us.keep posting .We decode everything that amplifies your brand and design some of the best logo designers in Chennai. For Enquiry Contact us @+91 9791811111
expert logo designers of chennai
logo makers in chennai
best logo designers in chennai
brand’s development company in chennai
logo creating service providers in chennai
best logo makers in chennai
In Latvia, the head of the government is Raimonds Vējonis. The government system of Latvia is a Parliamentary republic. In Latvia, the legislative power is vested in a Saeima; this is a Unicameral legislative body, and therefore a Unicameral Saeima. According to the World Bank Group, the government effectiveness index of Latvia is 0.97. This indicates that the government of Latvia is effective. Citizens enjoy well-organized public and civil services, and government efficiency is high. While some services may be lacking in certain areas, the overall environment fostered by government legislation is favorable.
Great post thanks for sharing such valuable list with us all. Such a nice content. We provide all social media services under cheap price with 100% real and active quality audience for tiktok, facebook, instagram etc... Buy instagram followers India
I have read your post, It's very informative and helpful for me. Often social media users searching for award winning Social Media Marketing Company in India and whole world, so they can Buy Real Instagram Followers Paytm.
Thanks for sharing nice post.
Commodity Tips and MCX Tips. | 100mcxtips.in
India's Top MCX Tips and Commodity Research Company
We provide 100% Returns in 18-24 Months
We provide Low Risk & High Growth Stocks
We provide 1 or 2 Multibagger Stock Ideas in a Year
We provide Dedicated Account and Relationship.
For More Detail Visit: - https://100mcxtips.in/
Great Research Solutions Pvt. Ltd. ( GRSoft ) is an IT company with no geographical boundaries and provides all that you can think of around IT including consulting, solutions, applications and outsourcing services.
Hire Software Developers
Great Research Solutions Pvt. Ltd. ( GRSoft ) is an IT company with no geographical boundaries and provides all that you can think of around IT including consulting, solutions, applications and outsourcing services.
Hire Software Developers
GRSoft Gaming is an honor winning, Live Casino game advancement organization of India. We offer curiosity and inventive game development with an exceptionally talented group of developer. Our bleeding edge gaming innovation creates esteem included gaming arrangements. Quality is our real worry for club game development. We offer tweaked Casino game development benefits over the globe and help you furnish with customized development. With our Casino game, individuals couldn't imagine anything better than to chance their gaining and appreciate the advantages. We have created numerous effective games like the video poker game, Sports wagering game, online club game, lottery games, and numerous other common games.
Hire Dedicated Casino Game Developers
GRSoft Gaming is an honor winning, Live Casino game advancement organization of India. We offer curiosity and inventive game development with an exceptionally talented group of developer. Our bleeding edge gaming innovation creates esteem included gaming arrangements. Quality is our real worry for club game development. We offer tweaked Casino game development benefits over the globe and help you furnish with customized development. With our Casino game, individuals couldn't imagine anything better than to chance their gaining and appreciate the advantages. We have created numerous effective games like the video poker game, Sports wagering game, online club game, lottery games, and numerous other common games.
Hire Dedicated Casino Game Developers
awesome article. thanks for sharing.keep posting like this.Escape your daily routine at the best Massage centre in Coimbatore. Family Friendly with lovely amenities and friendly staff. Book your Spa Massage today.
massage in coimbatore | body massage coimbatore | massage spa in coimbatore | body massage center in coimbatore | massage centre in chennai | body massage in chennai | massage spa in chennai | body massage centre in chennai | full body massage in chennai | chennai massage centre address
how to track a phone
hack boyfriend whatsapp
How to change your grades
how to hack into school systems
Is canon printer is offline mac error creating hindrance in your productive tasks? Need help from experts to resolve this error? If yes, then get in touch with our highly educated and skilled team. Who are available round the clock to help you. Our team will get you out of this error instantly. For more information visit the canon printer offline to know more.
This Jacket has been propelled by the amazing star ‘Tom Holland’. This Jacket has been produced by softened cowhide. It is accessible in darker shading. Thomas Stanley Suede Leather Jacket
Great Research Solutions Pvt. Ltd. ( GRSoft ) is an IT company with no geographical boundaries and provides all that you can think of around IT including consulting, solutions, applications and outsourcing services.
We are a combination of unmatched capabilities, experiences and jobs that serve across the industries. We knit closely with the clients to deliver high quality solutions with latest technologies and every growing business model approach. With the solutions provided by our professional staff our vision is to help our clients always reach new heights.
Software Development Company India | Software Development Company | Software Development Company usa | Software Development Consulting Services India
GRSoft Gaming is an honor winning, Live Casino game advancement organization of India. We offer curiosity and inventive game development with an exceptionally talented group of developer. Our bleeding edge gaming innovation creates esteem included gaming arrangements. Quality is our real worry for club game development. We offer tweaked Casino game development benefits over the globe and help you furnish with customized development. With our Casino game, individuals couldn't imagine anything better than to chance their gaining and appreciate the advantages. We have created numerous effective games like the video poker game, Sports wagering game, online club game, lottery games, and numerous other common games.
Casino Game Development Companies in India | Hire Poker Game Developers | Casino Game Developer | Casino Games Development Companies | Hire Poker Developers | Gaming Software Companies in India Rummy Game Software | Rummy Game Development
GRSoft's Remote IT infrastructure services are custom tailored based upon your business needs. Our Remote IT infrastructure services align network architecture and end-to-end communication, to ensure your company has the best IT solutions. We provide wide array of IT infrastructure services, right from IT infrastructure and consulting support to managing the most complex of IT infrastructural issues, with absolute precision.
Remote IT Infrastructure Support Services
GRSoft's Remote IT infrastructure services are custom tailored based upon your business needs. Our Remote IT infrastructure services align network architecture and end-to-end communication, to ensure your company has the best IT solutions. We provide wide array of IT infrastructure services, right from IT infrastructure and consulting support to managing the most complex of IT infrastructural issues, with absolute precision.
Remote IT Infrastructure Support Services
Your content is very attractive and useful. This is so amazing article. They are very helpful content. Thanks for sharing nice article. Rajasthan Budget Tours
how to hack your grades
I need a hacker urgently
cricket bet online is soaring in popularity thanks to the immense support for the game. While England may have ‘founded’ cricket, India is the world’s largest market for the sport, with the Indian Premier League acting as the biggest cricket league in the world. It also attracts a host of betting enthusiasts who are eager to place an online IPL satta.
Spying on other phones/devices is difficult isn't it?, not anymore. Visit the Ultimate spy site and get help from a professional hacker.
Read more on how to unlock iphone without passcode and check out the best Phone tracking app
Wow, Got know some of the best tricks and tips in this blog about flight deals… I booked my flight ticket on Porter Reservations and got the best flight deals and discounts which made my booking so much affordable and my flight journey comfortable.
Hello, Blog is full of information and content is also top quality and also useful… I was searching for the thrifty Christmas Flights Deals for my Christmas travel to my hometown I got it while booking online flight ticket.
Hello, I find while reading this blog that it’s very helpful for flyers searching for cheap flights… I made my last minute flight booking on Copa Reservations and got the cheap flight ticket and also earned reward points which I will use for my next flight ticket booking.
Hi, Very interesting blog and it have given all the important information for booking… Book your flight ticket in advance from Porter Airlines Official Site and avail the best discount & also earn reward points which can redeem later on.
I need a hacker urgently
I think the writer of this post is really good in terms of writing. I book my Delta International Flights from the Delta Airlines Official Site.
The post is providing complete information on this topic I really love to read this kind of content. JetBlue Reservations for US Booking can also done at Fares Match
The post is all about uniqueness and real facts and that’s why it is nice. Alaska Airlines Reservations is always an amazing choice for the US Travel.
I must say this blog is very nice according to me and I love this content. Turkish Airlines Official Site is the place to do the booking of Turkey and US Flights.
i need a hacker urgently
rent a hacker
Interpages
Guest Blogger
Guest Blogging Site
Guest Blogging Website
Guest Posting Site
Assignment task is an exceptionally requesting work a wide range of students. Furthermore, this is the motivation behind why various students are seen looking for somebody to do my assignment task! It is critical to have a decent ability of the scholastic order and comprehension of the multitude of ideas to chip away at the particular errand. From time to abilities they are falling behind big an ideal opportunity to have their review finished as expressed by their educators. In this way, here we come to help you with your requirements of somebody to do my assignment task. more- law assignment help , cheap assignment help
This is one of the most incredible blogs Ive read in a very long time.
vé máy bay đi úc tháng 2
cách săn vé rẻ đi hàn quốc
vé máy bay đi seoul vietjet
giá vé máy bay đi nhật bản vietjet
giá vé máy bay tphcm đi tokyo
Liechtenstein is located in Europe. Liechtenstein is considered to be a developed nation. The developmental stage of a nation is determined by a number of factors including, but not limited to, economic prosperity, life expectancy, income equality, and quality of life.
http://www.confiduss.com/en/jurisdictions/liechtenstein/business/company-formation/
Check out i need a hacker urgently Global Hackers Team offer the best service for cell phone tracking
Thank you for sharing such nice content so keep posting.
Alexa is not responding
Spying is not necessarily means you are trying to shatter someone’s peace and quiet. Considering today’s tendencies it’s obvious that parents worry about their children. Here is the solution. Go Hire a cell phone hacker to find more!
Nagaqq Yang Merupakan Agen Bandarq terbaik , Domino 99, Dan Bandar Poker Online Terpercaya di asia hadir untuk anda semua dengan permainan permainan menarik dan bonus menarik untuk anda semua
Bonus yang diberikan NagaQQ :
* Bonus rollingan 0.5%,setiap senin di bagikannya
* Bonus Refferal 10% + 10%,seumur hidup
* Bonus Jackpot, yang dapat anda dapatkan dengan mudah
* Minimal Depo 15.000
* Minimal WD 20.000
* Deposit via Pulsa TELKOMSEL
* 6 JENIS BANK ( BCA , BNI, BRI , MANDIRI , CIMB , DANAMON )
Memegang Gelar atau title sebagai AGEN POKER ONLINE Terbaik di masanya
Games Yang di Hadirkan NagaQQ :
* Poker Online
* BandarQ
* Domino99
* Bandar Poker
* Bandar66
* Sakong
* Capsa Susun
* AduQ
* Perang Bacarrat
* Perang Dadu (New Game)
Info Lebih lanjut Kunjungi :
Website : NAGAQQ
Facebook : NagaQQ official
WHATSAPP : +855977509035
Line : Cs_nagaQQ
TELEGRAM :+855967014811
BACA JUGA BLOGSPORT KAMI YANG LAIN:
Winner NagaQQ
Daftar NagaQQ
nagaqq
Nice post. I used to be checking constantly this blog and I am impressed! Extremely useful info particularly the ultimate section 🙂 I take care of such information a lot. I was seeking this certain information for a long time. Thank you and best of luck.
success essay
Great post! Once you order for our DNP Capstone Proposal help, we will certainly deliver errorless and plagiarism free Doctor of Nursing Practice capstone project.
Thank you for a great and inspiring blog post. I just want you to know that I enjoyed reading your post. Www.duluthseoagency.com
There's definately a lot to know about this issue. I really like all the points you made.
aprilia racing jackets
ducati leather jacket for sale
mens rose gold belt
victory motorcycle leather jacket
kawasaki green jackets
warriors vest costume
kawasaki racing suit
buy crop top for girls online from Dshred at easy prices delivered at your doorstep. Get free shipping
Dshred is proud to show you its collection of T-shirts and tops for women. We have a wide range of tops for girls, from Crop Tops to Tank Tops. Dshred has the greatest collection of tank tops for girls available online today. Get everything you need now for the perfect you, at Dshred.
The best trousers are in town only at Ndure. Log onto our site or visit our stores to get your hands on the best women trousers suitable for all occasions. Each trouser is manufactured keeping in mind comfort, luxury, and ease, casual hangouts. Ndure’s trousers for girls are the key to every day comfortability.
Dshred is proud to show you its collection of T-shirts and tops for girls. We have a wide range of tops for girls, from Crop Tops to Tank Tops. Dshred has the greatest collection of tank tops for girls available online today. Get everything you need now for the perfect you, at Dshred.
You can find Test Bank For Fundamentals Of Nursing 9e 9th Edition online in pdf/word format. Avail instant assistance for issues 24/7. There is no waiting time!
Gain better scores in every assignment and exam with Pediatric Primary Care 6th Edition Test Bank. Be on the top of your class.
There are various words including law, discipline, equity, right, and law, that are sufficient to push you. If so, employ our law assignment help administration and leave all such concerns on our experts' shoulders. assignment provider
amazing post thanks for the sharing beautiful post
everyone looking software agency
brisk logic is a software design app development and web design agency is located in Mohali India
web design
Buy Your Favorite Casual and Sports wear Quality Sports and Casual wears
Updated version of Test Bank For Legal Environment Of Business The 7 E available for instant download. Avail great discounts and offers now.
Hard exams, assignments and homework are a now things of the past with Solution Manual For Experiencing Mis Updated Second Canadian Edition Plus Mymislab With Pearson Etext Access Card Package 2 E 2nd Edition . Order and download now!
Abc do assignment in very unique and different way. The work is done on time and in an accurate position. So, everyone should take help of Abc expert team. assignment help
The secret for student success lies in the material you use for learning.Try Solution Manual For M Business 4th Edition and feel the difference.
College exams are not hard anymore! Face even the toughest tests and assignments with Solution Manual For Using Mis 8 E right away!
Nice Blog. Thanks for sharing with us. Such amazing information.
The modern trends in digital marketing during Covid-19 Pandemic
Thank you for posting such a great article! It contains wonderful and helpful posts. Keep up the good workMobile Prices Bangladesh
Best Medication Are Available For You. Just To Click And Order Now. Also, Have A Look On Our Website For the Best Blogs.
Modalert Dosage USA
Visit Website
Learning-10-best-pain-management-techniques-is-not-difficult-at-all-you-just-need-a-great-teacher
شركة درة البيت
شركة تنظيف في دبي
شركة تنظيف في ام القيوين
شركة تنظيف في الفجيرة
شركة تنظيف في العين
شركة تنظيف في عجمان
Love your writing and, love the your blogs and web pages! I will take these with me through my journey of being the best I can be! Thankyou to you, I got acquainted with what I was usually curious about this topics. I am thrilled with the quality posting and, I hope you have a nice day today. Thank you so much for this decent post and keep growing like this also in future. online paraphrasing tool - Assignment Help Australia - best assignment help in sydney - online assignment help melbourne
our online Law assignments specialists are profoundly qualified in the specific space of study and you can generally take its help to comprehend it well, which can help you clear your assessment with much better grades. Every single student who is studying the separate course needs to work upon various kinds of assignments and they just can't bear to take it nonchalantly on the grounds that it conveys a ton of grades. my assignment help
Dear admin, First of all, very good morning to you and your content writing team. I was impressed by your writing when i reading it. Your writing is impressive and so fresh. I want to write like you and, I hope you can read my post and let me know what to modify. I must spend a while finding out much more or figuring out more. Thank you so much for magnificent info about this topic and Good luck for your new posts. cpm homework help - essay help - math homework help - Assignment help
HACCP is abbreviated as Hazard Analysis Critical Control Points. It is a technique that is accepted internationally for preventing biological, chemical and physical hazards in the food safety system. The HACCP technique helps to establish critical control points, set critical limits, ensure control measures as well as to identify the risks for reducing the food safety hazards. HACCP Certification in Vietnam | PRP-OPRP | food safety through managing critical control points | Contact: enquiry@iascertification.com. Call @ +6531591803
Test banks and solution manuals are the best learning aids for any student. Try Moral Issues In Business 13th Edition Test Bank with instant download and unlimited access.
Looking for test banks and Solution Manuals online? Do not go any further! Just click on this link to access Test Bank For Entrepreneurship Successfully Launching New Ventures 6th Edition rightaway.
Exams are easier with the TestBank2022 assistance. Find best selling Test Bank For Physics 5th Edition and solution manuals and be on the top of your class today.
Higher education has never been easier with Solution Manual For Law And Ethics In The Business Environment 9th Edition available on TestBank2022 exclusively prepred to meet the needs of students aiming for top grades.
A scorpio rising woman knows how to use her sultry looks to drive a man crazy. She's very caring, loyal, and passionate in love.
Student needs are changing at an amazing rate now and dependency on online test banks and solution manuals are trending. TestBank2022 provides Solution Manual For Macroeconomics Principles Applications And Tools 10th Edition to help students acheive top grades at ease.
Thanks for writing this mind-blowing quality of article. Are you guys want to blow your professor’s mind by your quality assignment then contact essay typerfrom SourceEssay.
Test banks and solution manuals are the best learning aids for any student.
palm angels clothing
That is really an great web
colourist logo
amazing exactly what i was searching for great content keep up the good work.
Vlone shirt
Thank you for sharing the great information with us. this blog is
very good and informative.
ติดต่อ igoal88
nice post and article, best collection, will be thankful if you can share collection of websites which offers peshawari chappal. thank you so v.much
Assignment Help has proved to play the most influential role in education in today's scenario. However, students feel free after obtaining help from our helpers. Our helper's goal is to ensure that students do not think it pressures under a load of unnecessary things of completing various tasks on time by providing assignment assistance.
Detective Agency in Chennai
Builders in Chennai
Construction in Chennai
Building Construction in Chennai
Construction in Chennai
Building Renovation in Chennai
Construction Companies in Chennai
Civil Contractors in Chennai
CCTV Camera Services in Chennai
Hit Trans
Advocates in Chennai
Divorce Case Lawyers in Chennai
De Addiction Centre in Chennai
Spark Equipments
Office Cleaning Serviuces in Chennai
MKS Furniture
Mars Sterile
Sharetipsinfo is known for providing highly accurate Indian stock market tips which covers Cash tips, F&O intraday tips, Nifty intraday tips, Mcx intraday commodity tips and Share market tips with high accuracy.
#1 webdevelopment company
what an amazing article .Thanks for letting me post on your blog .We sell taurus guns at our site very affordable
You have performed a great job on this article, I like the helpful information you provided. I'll bookmark your blog and check again here frequently. I am quite certain I will learn a lot of new stuff right here! It’s very precise and highly qualitative. Thanks A lot. We are a small family-owned operated Kennels
that offers Mini & Standard Aussie Pups For Adoption, Our Aussiedoodles are ready now to go. Looking for a Reputable Breeder Locally Near
We are always concerned with the health, conformation, and temperament of all of our dogs.
Great post. I was checking continuously this blog and I am impressed! Very useful info specifically the last part :) I care for such info much. I was looking for this certain information for a very long time. Thank you and best of luck. Get It SMS is a India No 1 Bulk SMS Service Provider in Kolkata. Bulk SMS is considered to be the latest method to advertise and promote products and services. The far reaching impact of cell phones which have transformed the perception of communication as led to the popularity of this new marketing tool. Organisations pertaining to various sectors like Finance, retail, healthcare, automobile and many more are resorting to bulk SMS as a cheap, reliable, convenient and fast way to promote and advertise their products. Bengaluru with its open environment of welcoming change has taken the gamble and benefited by it. Various business houses based out of Bengaluru have witnessed positive results in the form of sales conversions. Moreover, Bulk SMS Service Provider in Delhi have managed to reach the right people with the right information and at the right time. Bulk SMS Service Provider in Mumbai has witnessed a success rate far higher than any other forms of marketing carried out in the city. A large part of this is attributed to the motley population residing in and around the city. These growing sections of IT professionals who migrate to this IT city every year have given it a distinct character. The lazy laid back environment that once characterised the place is being very soon replaced with a fast paced frenzy. People are becoming increasingly pressed for time. The conventional marketing techniques have long become back dated. Organisations therefore need to think of innovative methods to promote their products in order to remain in consumer memory. Bulk SMS is one such innovation that both organizers have adopted and consumers have accepted. Best OTP SMS Service Provider in India can your business to deliver the best services for your business all the time. So, if you look at the results of one time password SMS service. This has provided excellent service in security to the businesses.
check out this site cheap wigs human hair,wigs online,hair extensions,wigs,hair toppers,wigs for women,Lace Wigs,human hair toppers,hair pieces for women click this
Green Energy
Do you need a app that can hire a hacker to hack a phone? check this professional hackers out
This is such a great resource that you are providing and you give it away for free octobersveryownshop .
Nice blog and absolutely outstanding.https://palmangelsshop.com/ You can do something much better but I still say this is perfect. Keep trying for the best.
Thanks for the blog loaded with so many information. Stopping by your blog helped me to get what I was looking for.
corpsemerch.net
This is a very nice blogShop Here and learned more knowledge to read this post thanks for sharing this informative post.
mini dapple dachshund
Nice blog you have here. you can check crk jamb past question
Thanks for sharing this post with us.
Best Mini Ping Pong Table
Did you know that a Good Quotes can make a radical change in your life? So start reading Popular Quotes from today. Thank you.
My Homework Help is an established online academic platform that is famous for its progressive techniques related to helping countless students across the world with their homework and assignments and other related issues. Our site is renowned for its dedicated service to its customers and is recognized by Google as one of the best sites gaining trust and appreciation in Australia, the United States of America (USA), and the United Kingdom (UK). Our aim is not only to provide utmost assistance to the students in writing and analyzing their thesis paper but also to provide assistance to the students in solving academic computer science assignments (or homework) and its critical analysis.
Travis Goodspeed's blog is a great resource for tech enthusiasts. It's also important to prioritize our health, especially in cases of chronic viral bronchitis. Meri Sehat online medical services offer a convenient and reliable way to seek medical advice and manage chronic conditions from the comfort of our homes.
When you think of exams or assignments, think TestBank23, the top website to download Solution Manual For Business Statistics Global Edition 10th Edition hazzle free.
I am grateful to this blog for providing unique and helpful knowledge on this topic. Visit us for Getting online ib O level course with best tutors. Thank You!
Billionaire Boys Club Clothing Official Shop for BBC ICECREAM Fans. Get Amazing BBC Hoodies & BBC T-Shirts at Official EU Store.
"Thanks for sharing ths valuable content!.
I've found a web portal and APIs can be very useful when sending bulk SMS offers. The thing I like most about them is that they allow me to send really targeted messages based on specific criteria, which makes it easier for me to increase sales and customer satisfaction at the same time!
Click to know more:
bulk sms
bulk sms india
dlt registration "
White Spots on the Nails are a common cosmetic concern and are usually harmless. They are also known as leukonychia and can appear as small white dots, lines, or streaks on the nails.
Fungal infections of the nails can cause white spots, along with other symptoms such as thickening, discoloration, and crumbling of the nails.
Dreams can often be confusing and strange, and they can be influenced by our thoughts, feelings, and experiences. Seeing dead person alive in dream may be unsettling or even frightening, but it's important to remember that dreams are not always literal representations of reality.
The appearance of a dead person in a dream can be symbolic and may represent unresolved issues or emotions related to that person.
Aquarius Rising Sign Meaning people who known for their independent, unconventional, and intellectual approach to life.
They may enjoy exploring new and alternative ways of thinking and being, and they may be drawn to social causes that promote equality and justice.
Great blog post! Keep posting more updates like this! Thank You for sharing valuable thoughts with us! Hotel management is a complex and multifaceted field that involves the supervision & coordination of various activities related to hotel operations. As a hotel management student, you need to acquire knowledge & skills in several areas of the industry, including marketing, finance, operations & human resources. Many students enrolling in this course need to write management-related assignments. So, due to their busy plans, they cannot take the time to write the best tasks. In this situation, they seek the best Hotel Management Assignment Help USA Service Online from top skilled experts to obtain good marks.
Marriage Predictions by Date of Birth refer to the practice of using a person's date of birth to make predictions or interpretations about their potential marriage or marital life. It is a belief that certain astrological or numerological factors associated with a person's birth date can provide insights into their future marriage prospects, compatibility with a partner, or the timing of their marriage.
Get personalized insights into your life's journey from professional astrologers. Discover the hidden patterns, understand your strengths, and navigate challenges with confidence. Trust our experienced astrologers to provide accurate readings, birth chart analysis, and guidance on relationships, career, and personal growth. Unveil the secrets of the stars and unlock a deeper understanding of yourself with our expert astrological services.
Your in-depth analysis and insights into the vulnerabilities of the PHY layer shed light on the importance of maintaining robust security measures in our increasingly interconnected world.
https://www.promocodehq.com/blog/free-shein-gift-card/
Thank you for sharing your insights into remote exploitation techniques. Your blog post was informative and thought-provoking, and I appreciate the opportunity to briefly discuss Amy Roloff's notable accomplishments and net worth in this context.
amy roloff net worth
Cancer and Cancer Compatibility can often be described as harmonious, as they are likely to have similar needs and desires in a partnership. They both value security, home, and family, and are likely to prioritize creating a stable and loving environment. They can provide each other with the emotional support, care, and understanding that they both crave.
Unlock the secrets of the cosmos with the most accurate astrologers. Delve into their profound predictions and insightful guidance. Explore their proven track record of precise forecasts and tap into the wisdom of the stars. Experience the power of astrology with renowned astrologers known for their unparalleled accuracy. Trust in their expertise to illuminate your path and shape your future. Discover the world of astrology at its finest and embrace the profound insights offered by these exceptional astrological practitioners.
Leo and Capricorn Compatibility, represented by the lion, is a fire sign known for its confident, passionate, and charismatic nature. Leos tend to be natural leaders who enjoy being in the spotlight. They are generous, warm-hearted, and love to be admired and appreciated. Leos thrive on attention and recognition.
Cancer and Leo Compatibility can have a complex but potentially rewarding relationship. Their compatibility depends on their willingness to understand and appreciate each other's differences while finding a balance between emotional security and excitement. Open communication, mutual respect, and compromise are crucial for their relationship to thrive.
Cancer and Sagittarius Compatibility will need to communicate openly and honestly and should be mindful of each other's needs. Cancer should understand that Sagittarius needs freedom and space to explore, while Sagittarius should be more considerate of Cancer's need for emotional security and stability. Finding a balance between these two contrasting energies will be crucial for their compatibility.
Leo And Aquarius Compatibility, represented by the Water Bearer, is an independent and intellectual sign. Aquarians are often seen as unconventional and unique individuals who value their freedom and intellectual pursuits. They are known for their humanitarian nature, open-mindedness, and desire for intellectual stimulation.
Virgo and Capricorn Compatibility are both Earth signs, which means they have a practical and grounded approach to life. This shared element forms a strong foundation for their compatibility. Overall, Virgo and Capricorn tend to have a harmonious and stable relationship, characterized by loyalty, commitment, and a shared focus on achieving their goals.
Thank you for providing this information. Visit us for Getting Best Online English Language Courses at Affordable Prices.
Amazing Content with very useful information we are awaiting for your next blog.
>Certified vastu Astrologer
Amazing Content with very useful information we are awaiting for your next blog.
Vastu for Office
Amazing Content with very useful information we are awaiting for your next blog.
Astrology and horoscopes
Amazing Content with very useful information we are awaiting for your next blog.
astrologer for education horoscope online
Amazing Content with very useful information we are awaiting for your next blog.
kundli online 2023
Amazing Content with very useful information we are awaiting for your next blog.
Vastu for Factory
Global Assignment Help is a renowned organization that helps the students across the world by providing them with plagiarism-free assignments on time. The experts of the organization are highly qualified and dedicated to enhancing the quality of the assignments by adding correct and precise information about the concepts. They take care of the customisation provided by the students, maintaining the academic standards. Finally, the 24/7 customer service and affordable price makes them one of the best assignment help services in the world. Many students have gained benefit from the firm by choosing them, and scored high in their academics. Moreover with the best expert guidance and solutions, students can make their way to future success in their respective fields.
Amazing Content with very useful information we are awaiting for your next blog.
Govardhan Puja 2023
Amazing Content with very useful information we are awaiting for your next blog.
Best Vastu consultants
Amazing Content with very useful information we are awaiting for your next blog
Certified vastu Astrologer
Amazing Content with very useful information we are awaiting for your next blog
kundli online 2023
Amazing Content with very useful information we are awaiting for your next blog
11 Things to Do on Friday
Amazing Content with very useful information we are awaiting for your next blog
Vastu Vibes
Amazing Content with very useful information we are awaiting for your next blog
Dangers of Not Avoiding These 6 Things On Saturday
Amazing Content with very useful information we are awaiting for your next blog
Sunday holds significant importance
Your blog on remotely exploiting the PHY layer is an eye-opener to potential vulnerabilities. It's like shining a light on the hidden risks in wireless communication. And just as we need to stay vigilant in the digital world, we can also stay stylish and safe with #How to Stack Coupons on Shein when shopping for tech accessories. Thanks for the insightful content and the reminder to prioritize security!
Amazing Content with very useful information we are awaiting for your next blog.
best astrologer online
You have given amazing content with very useful information, we are waiting for your next blog.
Christmas2023
Amazing Content with very useful information we are awaiting for your next blog
Baby boy names starting with letter F
Amazing Content with very useful information we are awaiting for your next blog
Baby boy names starting with letter H
Amazing Content with very useful information we are awaiting for your next blog
Baby Boy Names Starting with Letter J
Amazing Content with very useful information. We are awaiting for your next blog.
birth chart calculator
Amazing content with extremely useful information. We are waiting for your next blog.
Baby boy names starting with the letter A
Amazing Content with very useful information we are awaiting for your next blog.
Astrology and Horoscope 2024
Amazing content with extremely useful information. We are waiting for your next blog.
Baby Boy Names with the Letter C
Amazing Content with very useful information we are awaiting for your next blog.
राशियों के आधार पर 2024 में वाहन खरीदने का समय
Amazing Content with very useful information we are awaiting for your next blog.
Holiday List 2024
Amazing Content with very useful information we are awaiting for your next blog
Certified Vastu Astrologer in Delhi NCR
Amazing Content with very useful information we are awaiting for your next blog
Virgo Love and Relationship Horoscope 2024
Amazing Content with very useful information we are awaiting for your next blog
Aquarius Love and Relationship Horoscope 2024
Amazing Content with very useful information we are awaiting for your next blog
best astrologer online in Delhi
Amazing Content with very useful information we are awaiting for your next blog
Vivah Muhurat 2024
Amazing Content with very useful information we are awaiting for your next blog
Shahrukh Khan Horoscope
It's quite helpful that you broke out the New York State Divorce Forms. It is clear that you desire to help people through a difficult journey. We greatly appreciate your help and clarity.New York State Divorce Forms
Jewelgalore features a captivating collection of couple rings , perfect for expressing your love and commitment. Explore our beautifully crafted pieces, symbolizing unity and shared moments.
Pursuing an mbbs medical? Osh University offers an exceptional educational experience, making it the preferred choice for aspiring medical professionals seeking quality and excellence.
Shalamar Hospital is your go-to destination for dermatological care. Our skilled skin specialist offer a wide range of services, ensuring your skin's health.
Amazing Content with very useful information we are awaiting for your next blog
Best Astrologers in USA
Amazing Content with very useful information we are awaiting for your next blog
Vastu for Office
As that paper is restricted to a formal, scholastic style, I might want to make a move to portray the strategy here in my kin's local language, which has absolutely no part of that formal drivel and high-faluttin' wordsmithin'. This being simply a mystery, if it's not too much trouble, read the paper for full specialized subtleties.
The thought is this: Layer 1 radio conventions are weak infusions like those that plague innocently carried out SQL sites. You can put one parcel within another bundle and have the internal parcel drop out to turn into its very own casing. We call the method Bundle in-Parcel, or PIP for short.
traffic lawyer mecklenburg va
Jewelgalore offers a captivating collection of ladies rings . Explore their exquisite designs, each a symbol of elegance and sophistication, perfect for adding a touch of luxury to your style.
Visit my page. stafford traffic lawyer
taper fade alto Thank you ever so for you blog. Really looking forward to read more
My partner and i bookmared your internet site a couple of days ago coz your blog impresses me personally FlixHQ.
The thought is this: Layer 1 radio conventions are weak infusions like those that plague innocently executed SQL sites. You can put one bundle within another parcel and have the internal bundle drop out to turn into its very own casing. We call the procedure Bundle in-Parcel, or PIP for short.charlottesville visitation lawyer
Remotely exploiting the physical layer (PHY) involves attacking vulnerabilities in the lowest layer of the OSI model, manipulating signals or transmissions to disrupt or compromise communication. This sophisticated attack vector requires deep understanding of wireless protocols and hardware intricacies, making it a potent but technically challenging method for cyber intrusion.This blog is a goldmine of information. Your blog packs a punch in just a few sentences. Your words are like gems. Thank you for sharing this! A quick, delightful read that left me inspired Thanks! "Your comment is like a burst of confetti, adding joy to our blog. Each word is a brushstroke on the canvas of conversation, creating a vibrant tapestry of ideas. We eagerly await your next insight, as your contributions light up our digital world. Thanks for being our comment superstar!" wape price
Hellstar Hoodies
Post a Comment